- Blog, Cloud
- Published on: 10.04.2026
- 4:40 min
Cloud security: How decentralization leads to greater responsibility
Cloud technologies have long been the backbone of modern corporate IT, making cloud security central to any IT strategy. The figures speak for themselves: never before has the threat landscape been so dynamic, the attack surface so large, and the importance of IT security as high as it is today.
Cyberattacks at record levels – the cloud in focus
The number of cyber incidents is reaching new highs every year. In Germany between 2024 and 2025 alone, the economic damage caused by cyber-attacks rose by more than 13% to over €200 billion. Alarmingly, around 45% of all security incidents involving data leakage now occur in the cloud (source: Exabeam). This is no coincidence, as the growing use of cloud services also increases the attack surface. At this point 81% of German companies rely on cloud solutions to scale their IT and drive digitalization forward (source: Bitkom). The increasing misuse of modern AI technologies further lowers the barriers to entry for attacks – a trend that further exacerbates the threat situation.
New organizational models, new risks
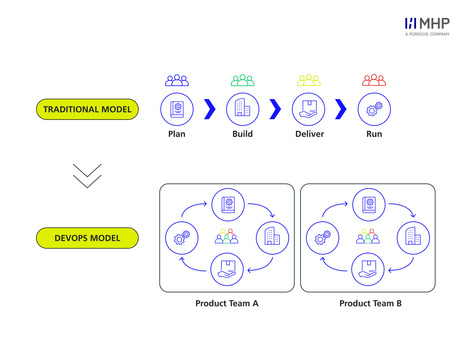
The cloud is not only changing technologies, but also the way companies operate IT. Traditional, centrally controlled IT teams are increasingly being replaced by smaller, autonomous DevOps teams. This increases flexibility and accelerates innovation, but also harbors new risks.
The decentralization of infrastructure
Distributing responsibility across multiple small teams – enables tailor-made solutions, but also increases complexity and potential errors. The most common causes of security incidents in the cloud today include misconfigurations and weaknesses in identity and access management (IAM). Overly broad access permissions and a lack of security awareness can create undetected vulnerabilities that put entire data sets at risk.
Cloud security: Different from On-Premises
A key difference to traditional IT: Although fine-grained segmentation is also possible in on-premises environments, it is often much easier and more consistent in the cloud, as modern platforms provide standardized and scalable functions. Microsegmentation and precise access rights are central to the zero-trust approach. However, these advantages only apply if they are implemented consistently. Misconfigurations in the cloud can inadvertently affect larger resource areas and cause risks to spread rapidly.
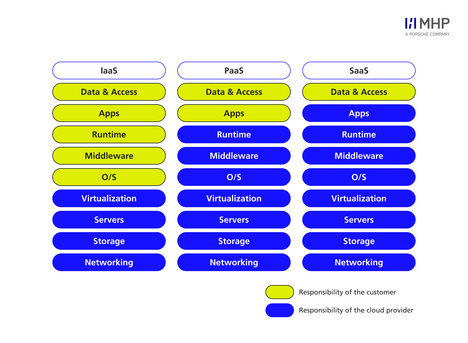
Shared Responsibility: Security is a Team Effort
Cloud security is not a given. The shared responsibility model dictates that while providers protect the hardware and visualization layers, customers are responsible for their own data and access controls. Whether using IaaS, PaaS, or SaaS, the specific boundaries shift, but the ownership of data security is never fully outsourced.
Companies also need to rethink their security processes and responsibilities. With the introduction of DevOps, shared responsibility within the company is also changing: Instead of clearly defined individual teams for infrastructure, development, or operations, cross-functional teams now work together and bear significantly more end-to-end responsibility – including secure configurations, operational processes, and continuous risk management. A decentralized DevOps organization can only close the security gap when it is deeply embedded within the teams and actively practiced by everyone involved.
Modern tools: CSPM, CWPP & CNAPP
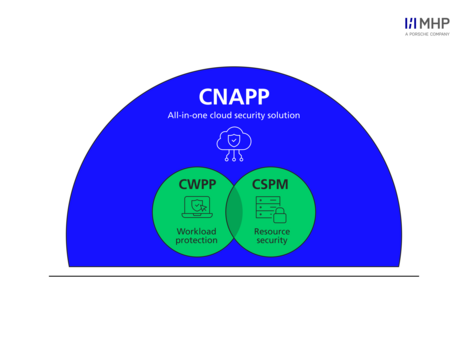
The dynamics and complexity of modern cloud environments require new tools. Traditional security reviews alone are no longer sufficient in identifying risks at an early stage, as infrastructure, systems, and configurations in the cloud are constantly changing. This has the knock-on effect of causing static controls to quickly become obsolete or no longer provide effective protection. Here, specialized solutions come into play:
- Cloud Security Posture Management (CSPM): Continuously monitors the cloud environment for misconfigurations and compliance violations.
- Cloud Workload Protection Platforms (CWPP): Monitor running workloads such as virtual machines, containers, and serverless functions and continuously check them for security-related deviations – such as unauthorized process executions, vulnerabilities, or suspicious activities within a container.
- Cloud Native Application Protection Platforms (CNAPP): Combine the strengths of CSPM, CWPP, and other tools to provide a holistic view of cloud security.
This selection covers the most important tool categories, but does not represent the entire spectrum of modern cloud security solutions. The tools help companies identify vulnerabilities early on, meet compliance requirements, and maintain control over their cloud assets.
Conclusion: Security is not a state, but a process
Beyond restructuring, the decentralization of modern IT organizations is shifting security ownership directly to teams. This is the deciding factor in whether cloud usage remains a risk or becomes a success factor: The more autonomy individual teams enjoy, the more critical clear responsibilities, automated security processes, and a deeply rooted awareness of security become. Modern cloud security tools such as CSPM, CWPP, and CNAPP help to reliably fulfill these new responsibilities and identify risks at an early stage.
To fully leverage the cloud, security should not be seen as an obstacle, but as an essential building block to make decentralization successful, resilient, and future-proof.
Do you have any questions? Get in touch with us – we'll be happy to advise you.
FAQs
Cloud technologies have become the backbone of modern enterprise IT. The threat landscape is more dynamic and the attack surface larger than ever before. In Germany in particular, the economic damage caused by cyberattacks is steadily increasing, and around 45% of all data breaches now occur in the cloud. With the increasing use of cloud services, the importance of IT security is also growing.
The cloud is changing not only technologies, but also organizational models. Traditional, centrally controlled IT teams are being replaced by smaller, autonomous DevOps teams. This increases flexibility, but also poses new risks: responsibility is distributed among many small teams, which increases complexity and the risk of errors. Misconfigurations and weaknesses in identity and access management are now among the most common causes of security incidents in the cloud.
Cloud security is a collaborative process based on the shared responsibility model: the cloud provider protects the physical infrastructure, while the company is responsible for the secure configuration and protection of its own data. Modern tools such as CSPM, CWPP, and CNAPP help identify risks early on, meet compliance requirements, and provide decentralized teams with a means of self-evaluation. A holistic approach with clear responsibilities, security by design, and consistent automation is crucial.
Static controls are no longer sufficient in the cloud because modern cloud environments are highly dynamic: infrastructure, configurations, and permissions are constantly changing. As a result, one-time or infrequent checks quickly become outdated and cannot reliably detect misconfigurations or compliance violations. Only through continuous, automated monitoring can risks be identified early and addressed effectively.